When we talk about online anonymity, most people immediately think of the Tor Browser. However, in the deep corners of the cybersecurity world, there is a more mysterious and robust layer known as I2P (Invisible Internet Project).
In 2026, as surveillance technology becomes more advanced, hackers and privacy advocates are shifting away from traditional methods to I2P. But why is this network so effective at hiding tracks, and what makes it different from everything else? Let’s dive deep into the shadows.
Understanding I2P Network Anonymity?
I2P is a decentralized, peer-to-peer network layer designed to allow users to communicate anonymously. Unlike the surface web, every connection on I2P is end-to-end encrypted. It creates a “network within a network,” often referred to as the Darknet.
While Tor was designed to access the “Clear Web” anonymously, I2P was built from the ground up to host hidden services (e-sites) and facilitate secure, private communication between peers.
The Secret Sauce: Garlic Routing
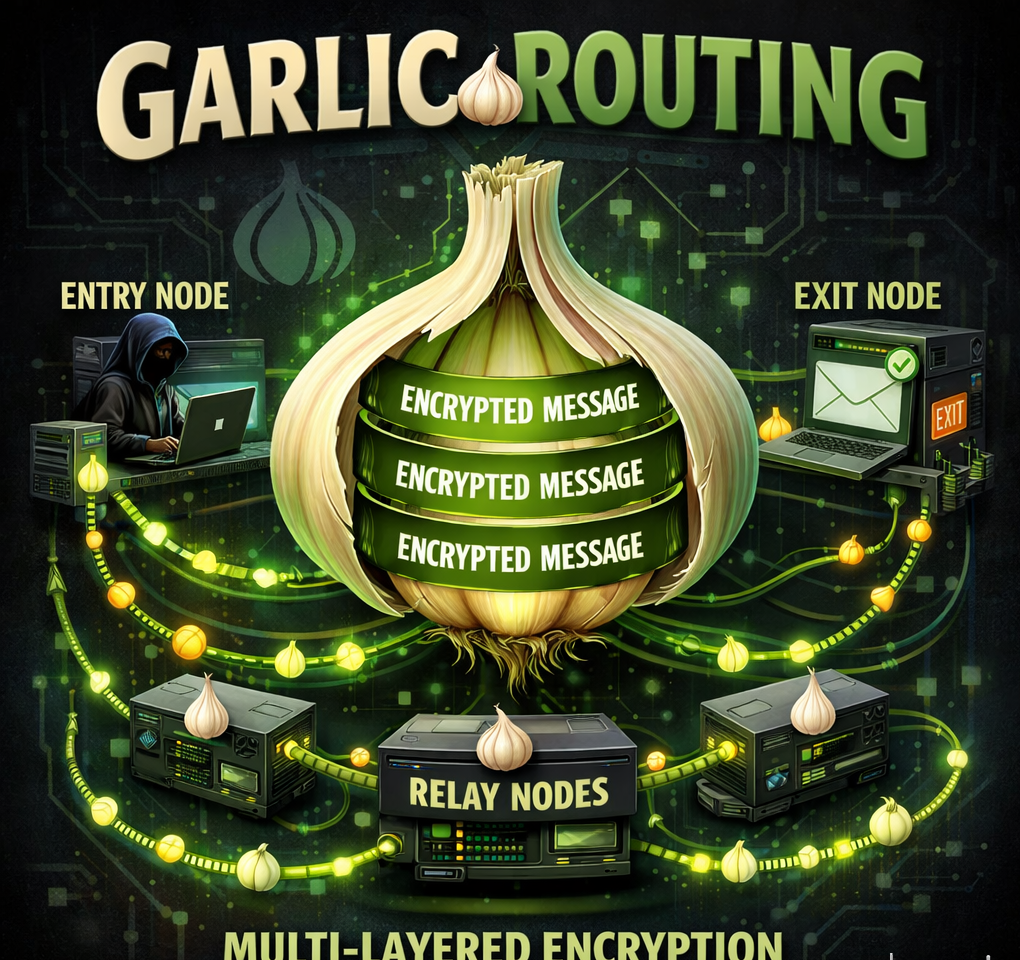
The primary reason hackers prefer I2P is its unique routing technique called Garlic Routing.
If you know Tor, you’ve heard of “Onion Routing,” where data is wrapped in multiple layers of encryption. I2P takes this a step further. In Garlic Routing, multiple messages (called “cloves”) are bundled together into a single encrypted packet.
This makes “Traffic Analysis” almost impossible. Even if an adversary monitors a piece of the network, they cannot tell which message is going where or what is inside the “garlic bulb.”
How to Detect I2P Network Anonymity Traffic
For a System Administrator, detecting I2P traffic is a challenge because it’s designed to look like normal encrypted traffic. However, there are a few signs to watch for:
- High P2P Activity: I2P relies on a high number of peer-to-peer connections. If a single workstation is maintaining hundreds of simultaneous UDP/TCP connections, it might be an I2P node.
- Traffic Patterns: Unlike standard HTTPS traffic, I2P traffic is constant and doesn’t follow typical human browsing patterns.
- Port Monitoring: While I2P can use any port, it often uses specific ranges that can be identified via deep packet inspection (DPI) tools.
Understanding these patterns is the first step in protecting your infrastructure from unauthorized hidden network usage.
Why Hackers Prefer I2P Over Tor?

For a System Administrator or a Security Professional, understanding the difference is crucial. Here is why the “Black Hat” community often chooses I2P:
- Fully Decentralized: Tor relies on a set of directory servers to manage the network. I2P has no central servers. Every user’s computer acts as a node, making it nearly impossible to “shut down” or block.
- Unidirectional Tunnels: In I2P, the data coming in and the data going out travel through different paths (tunnels). If a hacker is communicating with a server, the “Request” and the “Response” never take the same route.
- Built for P2P: I2P is optimized for file sharing and peer-to-peer communication, which is ideal for distributing tools or leaked data without being traced.
- Hidden from ISPs: Because I2P uses a variety of different protocols to transport data, it is much harder for an Internet Service Provider (ISP) to detect that someone is even using the network compared to Tor.
The Modern Admin’s Perspective
As a System Administrator, why should you care about I2P?
Understanding these hidden networks is part of Threat Intelligence. Hackers often use I2P to host Command & Control (C2) servers for malware. If your corporate network starts showing strange, encrypted peer-to-peer traffic, it could be a sign that an I2P tunnel is being used to exfiltrate data. Keeping an eye on these emerging patterns is what separates a basic admin from a security expert.
Conclusion
I2P is a powerful tool. While it is used by hackers for anonymity, it is also a vital resource for journalists and whistleblowers in oppressive regimes. In 2026, the battle for privacy is being fought in these hidden tunnels. As we advance, staying informed about these technologies is the only way to keep our own infrastructures secure.
